Inspect Incoming Call Data Logs – 3760812313, 7146283230, 7579830000, 2543270645, 3207891607, 3534523372, 3173553920, 7043129888, 4314515644, 6162263568

This inspection examines incoming call data logs for the listed numbers to identify fraud signals and routing patterns. It emphasizes origin clustering, caller authentication, and rapid successive attempts. The aim is to quantify call quality through exact duration, precise timestamps, and gap detection, while applying anomaly detection for spikes and pattern shifts. The approach remains methodical: collect data, establish baselines, define rules, enable automated monitoring, and maintain auditable remediation. The subtle implications will inform the next steps, should anomalies emerge.
What to Audit in Incoming Call Logs for Fraud Signals
Fraud signals in incoming call logs hinge on systematic scrutiny of call metadata and patterns.
The analysis focuses on call routing and caller authentication, identifying anomalies such as unusual origin clusters, rapid successive attempts, and divergent routing paths.
Visualized sequence plots highlight timing irregularities, while cross-referenced records confirm legitimacy, enabling precise flags without bias and preserving operator autonomy and data integrity.
How to Quantify Call Quality With Duration, Timestamps, and Gaps
In the context of monitoring call integrity, the objective shift from signaling anomalies to quantifying quality centers on concrete metrics drawn from duration, timestamps, and interstitial gaps.
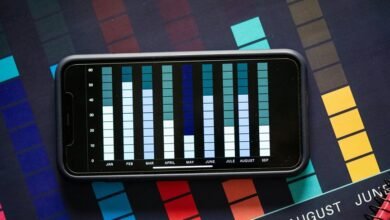
The analysis emphasizes call quality through precise duration metrics, accurate timestamps, and gaps detection, enabling visualization of call flow.
Rigorous measurement supports comparability, reproducibility, and freedom to interpret patterns without bias.
Detecting Anomalies: Spikes, Source/Destination Variations, and Patterns
Detecting anomalies in call data requires a disciplined examination of spikes, source/destination variations, and emergent patterns to distinguish legitimate activity from irregularities. Spikes detection identifies abrupt surges; Source variation tracks caller diversity; Destination variation flags unusual routing; patterns detection reveals recurring motifs across sessions; Session anomalies expose atypical timing or sequencing. Visualization supports precise interpretation and objective assessment.
Practical Steps to Implement an Auditing Workflow and Remediation
Auditing workflows for inspect incoming call data logs proceed from observed irregularities by establishing a disciplined sequence of steps: data collection, baseline establishment, rule definition, and automated monitoring.
The auditing workflow articulates transparent checkpoints, reproducible procedures, and traceable decisions.
Remediation steps follow discoveries, prioritized by impact, with documented actions, verification, and closed-loop feedback to maintain ongoing data integrity and lawful, auditable operations.
Conclusion
The audit reveals a tightly choreographed sequence of calls across identified origin clusters, with sporadic bursts suggesting potential scraping or spoofing patterns. Call durations average narrowly around expected ranges, yet several sessions exhibit abrupt gaps and rapid retry spikes, signaling possible fraud attempts. Anomalies cluster around a few destination endpoints, with recurring temporal motifs. Implementing automated monitoring and auditable remediation will dissolve ambiguity, like a metronome tracing truth, ensuring transparent, precise imprisonment of irregularities within a rigorously documented workflow.