Review Incoming Call Records for Verification – 3501414801, 8446600349, 6949475496, 8776206194, 18008290994, 7135537294, 8779140059, 18004982748, 8008225353, 3229124921

A structured review of incoming call records for verification is proposed, focusing on establishing baseline patterns for frequency, duration, geography, and caller ID consistency. The process will cross-check the listed numbers against logs and metadata, flagting deviations such as spikes or inconsistent routing. Quick, objective indicators will guide initial judgments, with findings documented and ownership assigned. Anomalies will be closed within one business day, supported by verifiable evidence to justify the final disposition, and a concise rationale will follow.
How to Identify Legitimate vs. Suspicious Call Patterns
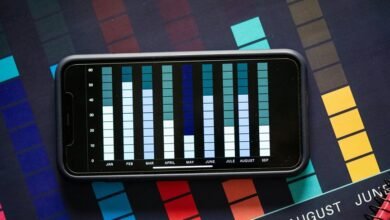
To distinguish legitimate from suspicious call patterns, analysts should first establish a baseline profile using historical data, including frequency, duration, geographic dispersion, and caller ID consistency.
The evaluation emphasizes meticulous pattern recognition, comparing deviations with documented norms.
Misleading cues may appear as abrupt frequency spikes or unusual call times; risk indicators include inconsistency in metadata and anomalous geographic clusters, prompting further verification.
Cross-Verification: Matching Logs, Caller IDs, and Metadata
Cross-verification involves a methodical reconciliation of logs, caller IDs, and metadata to confirm or challenge the authenticity of each call record. This process compares timestamped entries, tracing sequences across systems, and notes discrepancies in routing data. Findings emphasize cross verification and clear evidence trails, while caller metadata is evaluated for consistency with claimed numbers, locations, and device fingerprints.
Quick Checks to Validate Caller Intent Without Delays
Quick checks to validate caller intent without delays focus on rapid, structured assessment of signals that indicate genuine purpose. The approach separates legitimate patterns from volatile cues, prioritizing objective indicators such as caller behavior, context consistency, and corroborating metadata. Analysts catalog legitimate patterns while flagging suspicious patterns for immediate review, maintaining efficiency without compromising accuracy or safety.
Documenting Findings and Responding to Anomalies No Later Than the Next Business Day
Documenting findings and responding to anomalies within one business day requires a disciplined, auditable process. The procedure records observations objectively, assigns timestamps, and delineates ownership. Documentation remains concise, ensuring traceability without bias. Stakeholders benefit from consistent reporting standards. Mentioned elements avoid unrelated topic and irrelevant methods, promoting clarity. Anomalies are categorized, investigated, and closed with verifiable evidence, enabling timely, accountable decisions.
Conclusion
This evaluation follows a methodical, data-driven approach to outgoing call verification, aligning logs, IDs, and geolocation metadata against established baselines. Rapid indicators flag anomalies such as abrupt volume changes, routing inconsistencies, or mismatched caller IDs. Each finding is timestamped, ownership assigned, and supported by verifiable evidence for timely closure within one business day. The process functions like a meticulous compass, guiding investigators through a complex landscape to pinpoint deviations with objective precision.